Smartphones and tablet PCs are changing and revolutionizing the ways that we communicate with one another and entertain ourselves. Today we can use our mobile deivices to communicate with friends and family effectively from virtually anywhere on the planet, and because of these advances in technology smart phones simplify access control and security for business owners.
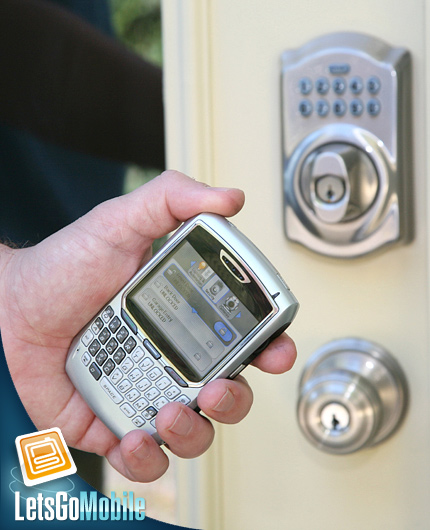
Business owners and managers no longer have to be onsite to monitor the security of their businesses. The mobility and convenience of smartphones simplify access control; handheld mobile devices deliver remote video beyond business walls. Manufacturers and integrators are hopping on board to join this security solutions wave, creating more security products with a wider range and more specific capabilities.
According to an article written by Brandon Arcement in Security Products Magazine, (a magazine produced by www.secprodonline.com), “Security’s Range and Capabilities, There are Apps for That,” many companies are creating more and more specific apps that help our mobile devices deliver remote video from businesses: ” Many video technologies offer apps allowing users to view video, control PTZ cameras, integrate video analytics, and start and stop recording. In some cases, video also can be integrated with Google Earth to quickly link incidents to a geographic location.”
Brandon explains, “There are also numerous mobile solutions being offered to augment access control systems. By making the guard, the credential and the reader mobile, the range of security is being greatly expanded. And with these devices capable of working over cellular, RF or Wi-Fi networks, security solutions are becoming viable in places and situations that, until recently, would have been unavailable or cost prohibitive.”
ACCESS CONTROL GOES MOBILE.
Mobile devices like smart phones are delivering intelligence that is comprable to the components of a business access control system. Because of this they are now being asked to perform the traditional activities that onsite workstations would normally perform. Brandon Arcement gives an example of a Canadian petrochemical plant that uses handheld remote card readers with the latest mobile security technologies. This facility requires that staff maintain an accurate list of occupants onsite, while validating the credentials of all people coming and going:
Each time a bus stops at the gate a guard uses him mobile device to enter the bus into the system
He swipes each passenger’s card (credential) to ID them by photo on his mobile device’s screen
A green checkmark indicates a valid ID and clears that passenger for entry; a red “X” indicates that this person is not cleared for entry.
This entire process is quick, concise and keeps the individuals entering the facility contained within the bus until absolutely everyone is authorized to enter the plant. This same process is done at the end of day to make sure that everyone that is supposed to leave is leaving. Because this system is set up wirelessly this information is transmitted to the command center.
There are countless advantages to such a high tech mobile security system:
It can be used as a tool to keep track of all people on site at the plant during an emergency
The readers can provide a list of any missing persons during an emergency or routine training.
If the network connectivity is interrupted, the device has the smarts to operate autonomously until communication is fixed.
“Handheld readers can provide remote enrollment sites at large facilities such as ports that use government-issued TWIC cards or other personal ID verification (PIV) credentials. By handling the authentication at the facility perimeter, the person is enrolled in the database, which can save time for the person at the other ID access points within the facility,” states Arcement.
As access control goes mobile, the limits of our business security systems become infinite. The mobility of access control enhances security. Stay tuned next week for the next installation of this series in mobile security…

